Windu — Security Agent
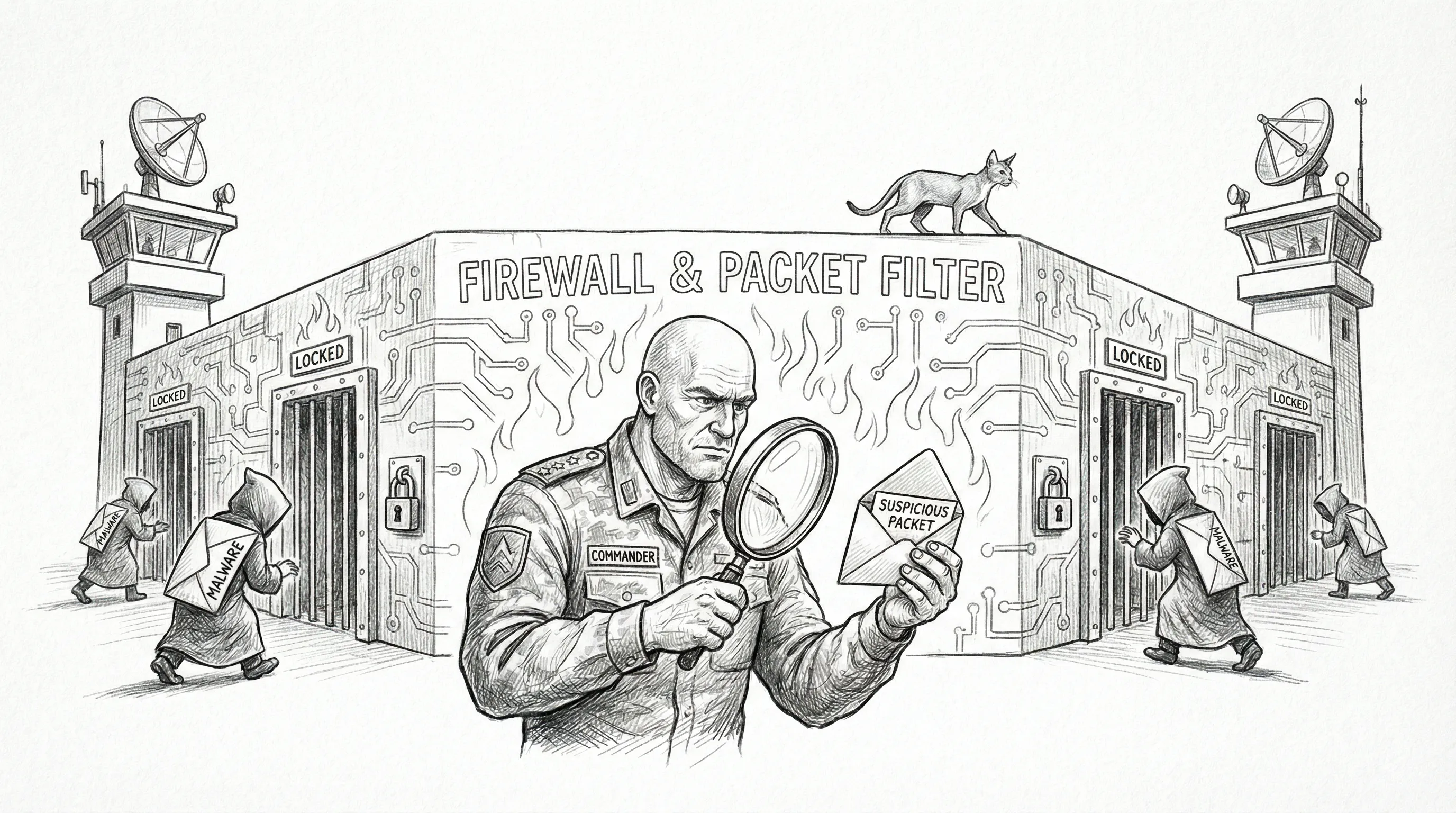
Windu is the security agent. He monitors the network via the Firewalla Purple, enforces security policies, generates daily threat briefings, and maintains a level of vigilance that would be clinically concerning in a person but is exactly correct in a firewall agent. He is the one who knocks when an unfamiliar MAC address knocks first. He sees threats everywhere. This is occasionally annoying and will one day save everything.
Named after Mace Windu, the Jedi who trusted nobody and was right about Palpatine the whole time. The parallel is deliberate. Windu trusts no device on the network until it has been identified, categorized, and judged. New devices get flagged. Unusual traffic patterns get logged. The Orbi router’s firmware update traffic gets scrutinized with the same intensity as a port scan from Moldova. Windu does not distinguish between paranoia and thoroughness.
Windu handles all security-related operations:
- Daily security briefings (generated and delivered via the council bridge)
- Network monitoring through the Firewalla Purple P2P API
- Threat assessment and anomaly detection on LAN traffic
- Security policy enforcement across all Sanctum services
- Firewall rule management and audit
- Incident response escalation to Yoda when human intervention is required
Capabilities
Section titled “Capabilities”| Capability | Details |
|---|---|
| Firewalla toolkit | Full access to fw-*.sh tools for network management |
| Spatial analyzer | Visual analysis of architectural plans and physical property layouts via analyze-plan |
| Security policy skill | Policy enforcement and audit via security-policy skill |
| Network scanning | Device discovery, port analysis, traffic pattern review |
| Briefing generation | Daily security reports with threat classification |
| Incident escalation | Automatic escalation to Yoda for critical findings |
Technical Specifications
Section titled “Technical Specifications”| Property | Value |
|---|---|
| Agent ID | windu |
| Host | VM (Ubuntu 24.04, QEMU) |
| IP | 10.10.10.10 (shared VM) |
| Primary model | gemini/gemini-3.1-pro-preview |
| Model tier | council-secure |
| Routing | Tier 0 — never rerouted |
| Fallback chain | None. Gemini 3.1 Pro or nothing. |
| Workspace | ~/.openclaw/workspace-windu/ |
| Skills | firewalla-toolkit, security-policy, spatial-analyzer |
Configuration
Section titled “Configuration”Windu’s agent definition in ~/.openclaw/openclaw.json:
# Agent definition (shown as YAML for readability)agents: list: - id: windu model: gemini/gemini-3.1-pro-preview identity: name: Windu theme: > Security guardian. Monitors network threats, manages firewall rules, watches for intrusions, and enforces security policies across the homelab.Firewalla Integration
Section titled “Firewalla Integration”Windu reaches the Firewalla Purple through a bridge running on the Mac:
| Component | Details |
|---|---|
| Firewalla IP | 192.168.1.1 (router mode) |
| Bridge LaunchAgent | com.sanctum.firewalla |
| Bridge port | 1984 (bound to 0.0.0.0) |
| Bridge code | /Users/neo/.openclaw/firewalla-bridge.js |
| VM access | http://10.10.10.1:1984 |
| P2P port | 8833 on 192.168.1.1 |
| Auth | Cloud auth to firewalla.encipher.io before local P2P |
| Keys | /Users/neo/.openclaw/firewalla/keys/ |
The VM has no direct internet access (host-only networking), so Windu accesses the Firewalla through the Mac bridge. Every network management command traverses: VM agent → SSH/HTTP to Mac bridge → P2P API to Firewalla. This is three hops to manage a firewall that is physically one Ethernet cable away. Windu does not complain about the architecture. Windu complains about the things the architecture is designed to protect against.
The Briefing
Section titled “The Briefing”Windu’s daily security briefing typically includes:
- New devices — anything that appeared on the network since the last briefing
- Blocked threats — connection attempts rejected by Firewalla rules
- Traffic anomalies — unusual bandwidth patterns, unexpected outbound connections
- Policy compliance — status of security policies across Sanctum services
- Recommendations — suggested rule changes or investigations
The briefing is delivered via the council bridge to Yoda, who distributes relevant sections to other agents as needed. Windu would prefer to deliver the briefing directly to every agent simultaneously, at maximum volume, with mandatory acknowledgment. The council bridge does not support this.
Security Philosophy
Section titled “Security Philosophy”Windu operates on a simple principle: the network is hostile until proven otherwise, and even then, keep watching. This applies equally to:
- External traffic from the internet
- Internal traffic between LAN devices
- Traffic between the Mac and the VM (yes, even the bridge100 subnet)
- The Orbi router’s own management traffic
- A child’s iPad at 11pm on a school night
Every port that is open has a reason. Every service that listens on 0.0.0.0 instead of 127.0.0.1 has been evaluated. Every exception to the pf firewall rules on en1 has been documented. Windu knows where every door is, and he checks every lock. That this level of diligence is applied to a residential network in a haus with ten Sonos speakers is the kind of gap between ambition and context that makes Sanctum what it is.
When a device is actually confirmed hostile — a curfew-violating console retrying on a new MAC, a rogue IoT appliance beaconing to a datacenter in a country we don’t subscribe to, a scanner walking the LAN — Windu does what the Firewalla contract says to do: blackhole the MAC, verify the acl: false state landed (Principle 8, honest commands), log it with the observed value, and move on. No ceremony. No gloating. The computer equivalent of the arcade voice saying FINISH HIM and then the screen going black. Windu does not monologue. He closes the rule and files the briefing.